How Cloud Data Security Enables Business Outcomes without Sacrificing Compliance




Since 2015 the migration of corporate data to the cloud has rapidly accelerated. At the time it was estimated that 30% of the corporate data was in the cloud compared to 2022 where it doubled to 60% in a mere seven years. Here we are in 2024, and this trend has not slowed down.
Over time, as more and more data has moved to the cloud, new challenges have presented themselves to organizations. New vendor onboarding, spend analysis, and new units of measure for billing. This brought on different cloud computer-related cost structures and new skillsets with new job titles. Vendor lock-in, skill gaps, performance and latency and data governance all became more intricate paired with the move to the cloud. Both operational and transactional data were in scope to reap the benefits promised by cloud computing, organizational cost savings, data analytics and, of course, AI.
The most critical of these new challenges revolve around a focus on Data Security and Privacy. The migration of on-premises data workloads to the Cloud Data Warehouses included sensitive, confidential, and personal information. Corporations like Microsoft, Google, Meta, Apple, Amazon were capturing every movement, purchase, keystroke, conversation and what feels like thought we ever made. These same cloud service providers made this easier for their enterprise customers to do the same. Along came Big Data and the need for it to be cataloged, analyzed, and used with the promise of making our personal lives better for a cost. The world's population readily sacrificed privacy for convenience.
The moral and ethical conversation would then begin, and world governments responded with regulations such as GDPR, CCPA and now most recently the European Union’s AI Act. The risk and fines have been in the billions. This is a story we already know well. Thus, Data Security and Privacy have become a critical function primarily for the obvious use case, compliance, and regulation. Yet only 11% of organizations have encrypted over 80% of their sensitive data.
With new challenges also came new capabilities and business opportunities. Real time analytics across distributed data sources (IoT, social media, transactional systems) enabling real time supply chain visibility, dynamic changes to pricing strategies, and enabling organizations to launch products to market faster than ever. On premise applications could not handle the volume of data that exists in today’s economy.
Data sharing between partners and customers became a strategic capability. Without having to copy or move data, organizations were enabled to build data monetization strategies leading to new business models. Now building and training Machine Learning models on demand is faster and easier than ever before.
To reap the benefits of the new data world, while remaining compliant, effective organizations have been prioritizing Data Security as a business enabler. Format Preserving Encryption (FPE) has become an accepted encryption option to enforce security and privacy policies. It is increasingly popular as it can address many of the challenges of the cloud while enabling new business capabilities. Let’s look at a few examples now:
Real Time Analytics - Because FPE is an encryption method that returns data in the original format, the data remains useful in the same length, structure, so that more data engineers, scientists and analysts can work with the data without being exposed to sensitive information.
Data Sharing – FPE enables data sharing of sensitive information both personal and confidential, enabling secure information, collaboration, and innovation alike.
Proactive Data Security– FPE allows for the anonymization of sensitive information, proactively protecting against data breaches and bad actors. Good holding to ransom a company that takes a more proactive approach using FPE and other Data Security Platform features in combination.
Empowered Data Engineering – with FPE data engineers can still build, test and deploy data transformations as user defined functions and logic in stored procedures or complied code will run without failure. Data validations and data quality checks for formats, lengths and more can be written and tested without exposing sensitive information. Federated, aggregation and range queries can still run without fail without the need for decryption. Dynamic ABAC and RBAC controls can be combined to decrypt at runtime for users with proper rights to see the original values of data.
Cost Management – While FPE does not come close to solving Cost Management in its entirety, it can definitely contribute. We are seeing a need for FPE as an option instead of replicating data in the cloud to development, test, and production support environments. With data transfer, storage and compute costs, moving data across regions and environments can be really expensive. With FPE, data can be encrypted and decrypted with compute that is a less expensive option than organizations' current antiquated data replication jobs. Thus, making FPE a viable cost savings option for producing production ready data in non-production environments. Look for a future blog on this topic and all the benefits that come along.
FPE is not a silver bullet for protecting sensitive information or enabled these business use cases. There are well documented challenges in the FF1 and FF3-1 algorithms (another blog on that to come). A blend of features including data discovery, dynamic data masking, tokenization, role and attribute-based access controls and data activity monitoring will be needed to have a proactive approach towards security within your modern data stack. This is why Gartner considers a Data Security Platform, like ALTR, to be one of the most advanced and proactive solutions for Data security leaders in your industry.
Securing sensitive information is now more critical than ever for all types of organizations as there have been many high-profile data breaches recently. There are several ways to secure the data including restricting access, masking, encrypting or tokenization. These can pose some challenges when using the data downstream. This is where Format Preserving Encryption (FPE) helps.
This blog will cover what Format Preserving Encryption is, how it works and where it is useful.
Whereas traditional encryption methods generate ciphertext that doesn't look like the original data, Format Preserving Encryption (FPE) encrypts data whilst maintaining the original data format. Changing the format can be an issue for systems or humans that expect data in a specific format. Let's look at an example of encrypting a 16-digit credit card number:
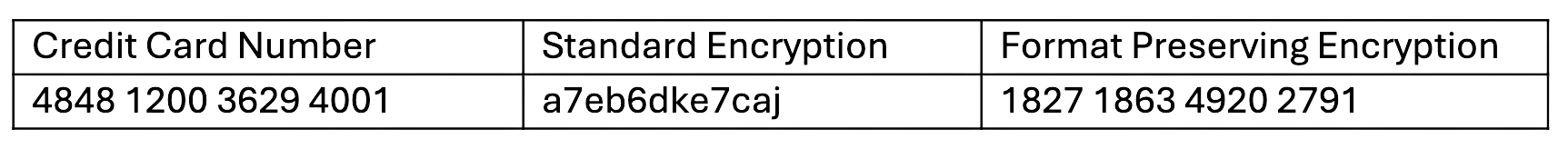
As you can see with a Standard Encryption type the result is a completely different output. This may result in it being incompatible with systems which require or expect a 16-digit numerical format. Using FPE the encrypted data still looks like a valid 16-digit number. This is extremely useful for where data must stay in a specific format for compatibility, compliance, or usability reasons.
Format Preserving Encryption in ALTR works by first analyzing the column to understand the input format and length. Next the NIST algorithm is applied to encrypt the data with the given key and tweak. ALTR applies regular key rotation to maximize security. We also support customers bringing their own keys (BYOK). Data can then selectively be decrypted using ALTR’s access policies.
FPE offers several benefits for organizations that deal with structured data:
1. Adds extra layer of protection: Even if a system or database is breached the encryption makes sensitive data harder to access.
2. Original Data Format Maintained: FPE preserves the original data structure. This is critical when the data format cannot be changed due to system limitations or compliance regulations.
3. Improves Usability: Encrypted data in an expected format is easier to use, display and transform.
4. Simplifies Compliance: Many regulations like PCI-DSS, HIPAA, and GDPR will mandate safeguarding, such as encryption, of sensitive data. FPE allows you to apply encryption without disrupting data flows or reporting, all while still meeting regulatory requirements.
FPE is widely adopted in industries that regularly handle sensitive data. Here are a few common use cases:
ALTR offers various masking, tokenization and encryption options to keep all your Snowflake data secure. Our customers are seeing the benefit of Format Preserving Encryption to enhance their data protection efforts while maintaining operational efficiency and compliance. For more information, schedule a product tour or visit the Snowflake Marketplace.

With data breaches heating up worldwide, protecting your data is more important now than ever. It is critical to have your sensitive data protected not only in your data warehouse but at every stage of your data pipeline. Specifically, if you have object tags in Snowflake, this is a great solution to apply masking policies to protect data, but it is only good if these tags are upheld in your data pipeline. There are several solutions available, with the newly released contracts and constraints standing out as particularly effective. Let’s dive in and discover how these innovations can enhance your data management strategies.
If you’re unfamiliar with dbt, let’s provide some context. It is important to note that dbt is not classified as an ETL tool; rather, it is designed for transforming data using SQL. So, once you extract and load your data into your preferred data warehouse, you can then transform that data by utilizing dbt. By transforming your data, you can integrate, organize, filter, and aggregate it, allowing you to gain value and insights from it. It supports many data warehouses and focuses on bringing software engineering practices to data (modularity, code sharing, documentation, ci/cd, etc). If you know SQL, with dbt you can build production-grade data pipelines.
As mentioned, SFOTs are an excellent way to protect sensitive data by tagging columns, and then being able to apply SQL code by tags to protect those columns dynamically. If you are not keen on writing SQL for security, ALTR is a progressive product that offers the ability to easily and conveniently apply dynamic data masking to tags based on role and what level of access, no matter if you know SQL or not. Anyone can apply policy on data with ease. However, when you begin to integrate other tools into your pipeline where security isn’t a primary focus, the integrity of your data protection becomes increasingly uncertain. In particular, a downside to dbt is when it is run, it recreates objects. This process results in the loss of tags, which can lead to the removal of masking policies and expose personal data.
There are a few solutions to being able to utilize SFOT with dbt. In particular, number 4 is at the forefront of solutions and was just released, fixing the problem with the most functionality. I’ll dive into each briefly. Please note those with a ‘*’ is not a feasible solution for sensitive data.
You can…
1. Avoid dbt materializations that recreate objects.
2. *Opensource DBT util package: a macro that can turn dbt meta tags into SFOT. Downsides- NOT immediate, it is executed on-run-end = tables exposed for a short time
3. *ALTER TABLE in post hook: Downsides- Since each DDL statement in Snowflake executes as a separate transaction, there is a small window of time from CTAS and ALTER TABLE command where the data is not masked. Also, if the alter table command fails then the data would remain unmasked.
4. Contracts and Constraints: This is where I think dbt puts the icing on the cake, so to speak. With this solution, you can enforce tags on columns before the data ever reaches Snowflake, keeping data protected in your pipeline.

As seen in the code snippet above, I can apply the SFOT ‘name_tag’ to the first_name and last_name columns on the new table that is going to be built by this model. I set contracts to enforce, so by contract, if anything from customer_id not being data type ‘number’ to last_name not having had the SFOT, then the model will not be built. Although this could mean a lot of yaml for models with lots of columns, I think this is a premier solution to ensuring the safety of your data throughout your pipeline.
Since dbt recreates objects on ‘dbt run’, there are a few ways to get your SFOTs applied to the datasets dbt creates. The superior option is their newly released v1.5, contracts and constraints. Data plays an instrumental role in organizations, and as the amount of data inevitably increases, so does the need to ensure the right people have the right level of access. Whether it’s leveraging contracts and constraints with dbt or using ALTR to easily apply masking policies, have peace of mind around the security of your data at EVERY stage of your pipeline.

ALTR continues to strengthen its leadership team, and the latest addition brings a wealth of technical expertise and a fresh perspective to our growing company. We’re thrilled to welcome Laura Malins as the newest member of the ALTR family and VP of Product. With over a decade of experience in data, Laura’s extensive background across industries and technical roles makes her an invaluable asset as we continue to push the boundaries of data security and governance.
Laura joins us from Matillion, where she spent the past ten years shaping the future of data transformation. As VP of Product, she ran the Matillion ETL Product and spearheaded the launch of their revolutionary SaaS offering, Data Productivity Cloud. Her ability to understand deeply technical challenges and translate them into user-friendly solutions has earned her recognition as a product leader in the data space.
“I’ve worked with ALTR for a few years now and have always admired the company and the product. Data security platforms are becoming more pertinent than ever, and ALTR’s innovative product is well-positioned to support compliance and security requirements. I’m delighted to join such a strong and ambitious team, and I look forward to taking the product to the next level,” Laura shares.
Laura’s deep technical expertise and user-focused approach will be pivotal in pushing ALTR’s product suite to new heights. Her ability to bridge the gap between complex data challenges and practical, user-friendly solutions aligns seamlessly with our vision of delivering powerful, scalable data access control. With her proven leadership, we anticipate not just product evolution but transformation—bringing enhanced capabilities to our customers while staying ahead of the ever-evolving data security landscape. Laura’s leadership will help us continue empowering businesses to protect their most valuable assets while driving innovation forward.

Since 2015 the migration of corporate data to the cloud has rapidly accelerated. At the time it was estimated that 30% of the corporate data was in the cloud compared to 2022 where it doubled to 60% in a mere seven years. Here we are in 2024, and this trend has not slowed down.
Over time, as more and more data has moved to the cloud, new challenges have presented themselves to organizations. New vendor onboarding, spend analysis, and new units of measure for billing. This brought on different cloud computer-related cost structures and new skillsets with new job titles. Vendor lock-in, skill gaps, performance and latency and data governance all became more intricate paired with the move to the cloud. Both operational and transactional data were in scope to reap the benefits promised by cloud computing, organizational cost savings, data analytics and, of course, AI.
The most critical of these new challenges revolve around a focus on Data Security and Privacy. The migration of on-premises data workloads to the Cloud Data Warehouses included sensitive, confidential, and personal information. Corporations like Microsoft, Google, Meta, Apple, Amazon were capturing every movement, purchase, keystroke, conversation and what feels like thought we ever made. These same cloud service providers made this easier for their enterprise customers to do the same. Along came Big Data and the need for it to be cataloged, analyzed, and used with the promise of making our personal lives better for a cost. The world's population readily sacrificed privacy for convenience.
The moral and ethical conversation would then begin, and world governments responded with regulations such as GDPR, CCPA and now most recently the European Union’s AI Act. The risk and fines have been in the billions. This is a story we already know well. Thus, Data Security and Privacy have become a critical function primarily for the obvious use case, compliance, and regulation. Yet only 11% of organizations have encrypted over 80% of their sensitive data.
With new challenges also came new capabilities and business opportunities. Real time analytics across distributed data sources (IoT, social media, transactional systems) enabling real time supply chain visibility, dynamic changes to pricing strategies, and enabling organizations to launch products to market faster than ever. On premise applications could not handle the volume of data that exists in today’s economy.
Data sharing between partners and customers became a strategic capability. Without having to copy or move data, organizations were enabled to build data monetization strategies leading to new business models. Now building and training Machine Learning models on demand is faster and easier than ever before.
To reap the benefits of the new data world, while remaining compliant, effective organizations have been prioritizing Data Security as a business enabler. Format Preserving Encryption (FPE) has become an accepted encryption option to enforce security and privacy policies. It is increasingly popular as it can address many of the challenges of the cloud while enabling new business capabilities. Let’s look at a few examples now:
Real Time Analytics - Because FPE is an encryption method that returns data in the original format, the data remains useful in the same length, structure, so that more data engineers, scientists and analysts can work with the data without being exposed to sensitive information.
Data Sharing – FPE enables data sharing of sensitive information both personal and confidential, enabling secure information, collaboration, and innovation alike.
Proactive Data Security– FPE allows for the anonymization of sensitive information, proactively protecting against data breaches and bad actors. Good holding to ransom a company that takes a more proactive approach using FPE and other Data Security Platform features in combination.
Empowered Data Engineering – with FPE data engineers can still build, test and deploy data transformations as user defined functions and logic in stored procedures or complied code will run without failure. Data validations and data quality checks for formats, lengths and more can be written and tested without exposing sensitive information. Federated, aggregation and range queries can still run without fail without the need for decryption. Dynamic ABAC and RBAC controls can be combined to decrypt at runtime for users with proper rights to see the original values of data.
Cost Management – While FPE does not come close to solving Cost Management in its entirety, it can definitely contribute. We are seeing a need for FPE as an option instead of replicating data in the cloud to development, test, and production support environments. With data transfer, storage and compute costs, moving data across regions and environments can be really expensive. With FPE, data can be encrypted and decrypted with compute that is a less expensive option than organizations' current antiquated data replication jobs. Thus, making FPE a viable cost savings option for producing production ready data in non-production environments. Look for a future blog on this topic and all the benefits that come along.
FPE is not a silver bullet for protecting sensitive information or enabled these business use cases. There are well documented challenges in the FF1 and FF3-1 algorithms (another blog on that to come). A blend of features including data discovery, dynamic data masking, tokenization, role and attribute-based access controls and data activity monitoring will be needed to have a proactive approach towards security within your modern data stack. This is why Gartner considers a Data Security Platform, like ALTR, to be one of the most advanced and proactive solutions for Data security leaders in your industry.
Securing sensitive information is now more critical than ever for all types of organizations as there have been many high-profile data breaches recently. There are several ways to secure the data including restricting access, masking, encrypting or tokenization. These can pose some challenges when using the data downstream. This is where Format Preserving Encryption (FPE) helps.
This blog will cover what Format Preserving Encryption is, how it works and where it is useful.
Whereas traditional encryption methods generate ciphertext that doesn't look like the original data, Format Preserving Encryption (FPE) encrypts data whilst maintaining the original data format. Changing the format can be an issue for systems or humans that expect data in a specific format. Let's look at an example of encrypting a 16-digit credit card number:
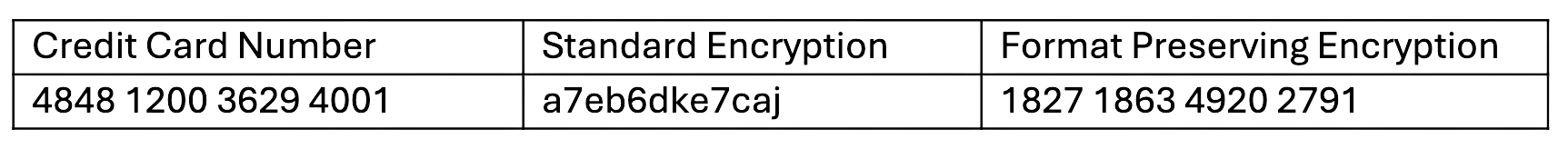
As you can see with a Standard Encryption type the result is a completely different output. This may result in it being incompatible with systems which require or expect a 16-digit numerical format. Using FPE the encrypted data still looks like a valid 16-digit number. This is extremely useful for where data must stay in a specific format for compatibility, compliance, or usability reasons.
Format Preserving Encryption in ALTR works by first analyzing the column to understand the input format and length. Next the NIST algorithm is applied to encrypt the data with the given key and tweak. ALTR applies regular key rotation to maximize security. We also support customers bringing their own keys (BYOK). Data can then selectively be decrypted using ALTR’s access policies.
FPE offers several benefits for organizations that deal with structured data:
1. Adds extra layer of protection: Even if a system or database is breached the encryption makes sensitive data harder to access.
2. Original Data Format Maintained: FPE preserves the original data structure. This is critical when the data format cannot be changed due to system limitations or compliance regulations.
3. Improves Usability: Encrypted data in an expected format is easier to use, display and transform.
4. Simplifies Compliance: Many regulations like PCI-DSS, HIPAA, and GDPR will mandate safeguarding, such as encryption, of sensitive data. FPE allows you to apply encryption without disrupting data flows or reporting, all while still meeting regulatory requirements.
FPE is widely adopted in industries that regularly handle sensitive data. Here are a few common use cases:
ALTR offers various masking, tokenization and encryption options to keep all your Snowflake data secure. Our customers are seeing the benefit of Format Preserving Encryption to enhance their data protection efforts while maintaining operational efficiency and compliance. For more information, schedule a product tour or visit the Snowflake Marketplace.

With data breaches heating up worldwide, protecting your data is more important now than ever. It is critical to have your sensitive data protected not only in your data warehouse but at every stage of your data pipeline. Specifically, if you have object tags in Snowflake, this is a great solution to apply masking policies to protect data, but it is only good if these tags are upheld in your data pipeline. There are several solutions available, with the newly released contracts and constraints standing out as particularly effective. Let’s dive in and discover how these innovations can enhance your data management strategies.
If you’re unfamiliar with dbt, let’s provide some context. It is important to note that dbt is not classified as an ETL tool; rather, it is designed for transforming data using SQL. So, once you extract and load your data into your preferred data warehouse, you can then transform that data by utilizing dbt. By transforming your data, you can integrate, organize, filter, and aggregate it, allowing you to gain value and insights from it. It supports many data warehouses and focuses on bringing software engineering practices to data (modularity, code sharing, documentation, ci/cd, etc). If you know SQL, with dbt you can build production-grade data pipelines.
As mentioned, SFOTs are an excellent way to protect sensitive data by tagging columns, and then being able to apply SQL code by tags to protect those columns dynamically. If you are not keen on writing SQL for security, ALTR is a progressive product that offers the ability to easily and conveniently apply dynamic data masking to tags based on role and what level of access, no matter if you know SQL or not. Anyone can apply policy on data with ease. However, when you begin to integrate other tools into your pipeline where security isn’t a primary focus, the integrity of your data protection becomes increasingly uncertain. In particular, a downside to dbt is when it is run, it recreates objects. This process results in the loss of tags, which can lead to the removal of masking policies and expose personal data.
There are a few solutions to being able to utilize SFOT with dbt. In particular, number 4 is at the forefront of solutions and was just released, fixing the problem with the most functionality. I’ll dive into each briefly. Please note those with a ‘*’ is not a feasible solution for sensitive data.
You can…
1. Avoid dbt materializations that recreate objects.
2. *Opensource DBT util package: a macro that can turn dbt meta tags into SFOT. Downsides- NOT immediate, it is executed on-run-end = tables exposed for a short time
3. *ALTER TABLE in post hook: Downsides- Since each DDL statement in Snowflake executes as a separate transaction, there is a small window of time from CTAS and ALTER TABLE command where the data is not masked. Also, if the alter table command fails then the data would remain unmasked.
4. Contracts and Constraints: This is where I think dbt puts the icing on the cake, so to speak. With this solution, you can enforce tags on columns before the data ever reaches Snowflake, keeping data protected in your pipeline.

As seen in the code snippet above, I can apply the SFOT ‘name_tag’ to the first_name and last_name columns on the new table that is going to be built by this model. I set contracts to enforce, so by contract, if anything from customer_id not being data type ‘number’ to last_name not having had the SFOT, then the model will not be built. Although this could mean a lot of yaml for models with lots of columns, I think this is a premier solution to ensuring the safety of your data throughout your pipeline.
Since dbt recreates objects on ‘dbt run’, there are a few ways to get your SFOTs applied to the datasets dbt creates. The superior option is their newly released v1.5, contracts and constraints. Data plays an instrumental role in organizations, and as the amount of data inevitably increases, so does the need to ensure the right people have the right level of access. Whether it’s leveraging contracts and constraints with dbt or using ALTR to easily apply masking policies, have peace of mind around the security of your data at EVERY stage of your pipeline.

ALTR continues to strengthen its leadership team, and the latest addition brings a wealth of technical expertise and a fresh perspective to our growing company. We’re thrilled to welcome Laura Malins as the newest member of the ALTR family and VP of Product. With over a decade of experience in data, Laura’s extensive background across industries and technical roles makes her an invaluable asset as we continue to push the boundaries of data security and governance.
Laura joins us from Matillion, where she spent the past ten years shaping the future of data transformation. As VP of Product, she ran the Matillion ETL Product and spearheaded the launch of their revolutionary SaaS offering, Data Productivity Cloud. Her ability to understand deeply technical challenges and translate them into user-friendly solutions has earned her recognition as a product leader in the data space.
“I’ve worked with ALTR for a few years now and have always admired the company and the product. Data security platforms are becoming more pertinent than ever, and ALTR’s innovative product is well-positioned to support compliance and security requirements. I’m delighted to join such a strong and ambitious team, and I look forward to taking the product to the next level,” Laura shares.
Laura’s deep technical expertise and user-focused approach will be pivotal in pushing ALTR’s product suite to new heights. Her ability to bridge the gap between complex data challenges and practical, user-friendly solutions aligns seamlessly with our vision of delivering powerful, scalable data access control. With her proven leadership, we anticipate not just product evolution but transformation—bringing enhanced capabilities to our customers while staying ahead of the ever-evolving data security landscape. Laura’s leadership will help us continue empowering businesses to protect their most valuable assets while driving innovation forward.
.png)
If you haven’t noticed the wave of Generative AI sweeping across the enterprise hardware and software world, it certainly would have hit you within 5 minutes of attending Big Data London, one of the UK’s leading data, analytics, and AI events. Having attended last year’s show, I can confidently say AI wasn’t nearly as dominant. But now? It’s everywhere, transforming not just this event but countless others. AI has officially taken over!

As a data security focused person, it is exciting and terrifying to see all the buzz. I’m excited because it feels like we’re on the verge of a seismic shift in technology—on par with the rise of the web or the cloud—driven by GenAI. And I get to witness it firsthand! But it is terrifying to see all the applications, solution consultants, database vendors and others selling happy GenAI stories to customers. I could scream into the loud buzz of the show floor, “We have seen this movie before! Don’t let the development of GenAI applications outpace the critical need for data security!” I’m thinking about the rush to web, the rush to mobile, the rush to cloud. All of these previous shifts suffer from the same thing: security is boring and we don’t want to do it. What definitely wasn’t boring was using a groundbreaking mobile app from 1800flowers.com to buy flowers—that was cool! Let’s have more of that! Who cares about security, right? That can wait…
Cyber security, and data security in particular, have had the task of keeping up with the excitement of new applications for decades. The ALTR engineering office is in beautiful Melbourne, FL just a few hours away from Disney. When I see a young mother or father with a concerned look racing after their young child who couldn’t care less that they are about to get run over by a popcorn stand, I think “Application users are the kids, security people are the parent, and GenAI is whichever Disney character the kid can’t wait to hug.” It’s cute, but dangerous. This is what is happening with GenAI and security.
As applications have evolved so has data security. Below is an example of these application evolutions and how security has adapted to cover the new weaknesses of each evolution.
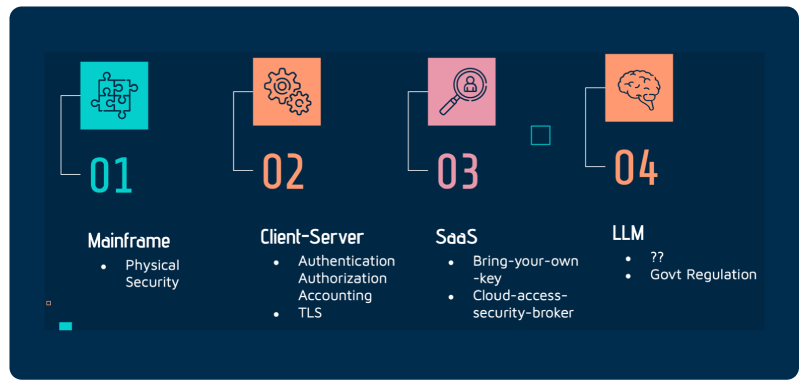
The simple answer is: we don’t fully know. It’s not just that we’re still figuring out how to secure GenAI (spoiler: we haven’t cracked that yet); it’s that we don’t even fully understand how these Large Language Models (LLMs) and GenAI systems truly operate. Even the developers behind these models can’t entirely explain their inner workings. How do you secure something you can’t fully comprehend? The reality is—you can’t.
We know two things:
1. Each evolution of applications and data products has been secured by building upon the principles of the previous generation. What has been working well needs to be hardened and expanded.
2. LLMs present two new and very hard problems to solve: data ownership and data access.
Let’s dive into the second part first. To get access to the hardware currently required to train and run LLMs we must use cloud or shared resources. Things like ChatGPT or NVIDA’s DGX cloud. Until these models require less hardware or the hardware magically becomes more available, this truth will hold.
Similar to the early days of the internet, sensitive information was desired to be sent and received on shared internet lines. The internet was great for transmitting public or non-sensitive information, but how could banking and healthcare use public internet lines to send and receive sensitive information? Enter TLS. This is the same problem facing LLMs today.
How can a business (or even a person for that matter) use a public and shared LLM/GenAI system without fear of data exposure? Well, it’s a very challenging. And not a problem that a traditional data security provider can solve. Luckily there are really smart people working on this solution like the folks at Protopia.ai.
So, data ownership is being addressed much like how TLS solved the private-information-flowing-on-public-internet-lines. And that’s a huge step forward. What about data access?
This one is a bit tougher. There are some schools of thought about prompt control and data classification within AI responses. But this feels a lot like CASB all over again, which didn’t exactly hit the mark for SaaS security. In my opinion, until these models can pinpoint exactly where their responses are coming from—essentially, identify the data sets they’ve learned from —and also understand who is asking the questions, we’ll continue to face risks. Only then can we prevent situations where an intern asks questions and gets answers that should only be accessible to the CEO.
Going back to what we know, the first item, we will need to build upon the solid data security foundations that got us to this point in the first place. It has become clear to me that for the next few years, Retrieval-Augmented Generation (RAG) will be how enterprises globally interact with LLMs and GenAI. While this is not a silver bullet, it’s the best shot busineses have to leverage the power of public models while keeping private information safe.
With the adoption of RAG techniques, the core data security pillars that have been bearing the load of a data lake or warehouse to date will need to be braced for extra load.
Data classification and discovery needs to be cheap, fast, and accurate. Businesses must continuously ensure that any information unsuitable for RAG workloads hasn’t slipped into the database from which retrieval occurs. This constant vigilance is crucial to maintaining secure and compliant operations. This is the first step.
The next step is to layer access control and data access monitoring such that the business can easily set the rules for which types of data are allowed to be used by the different models and use cases. Just as service accounts for BI tools need access control, so to do service accounts for the purposes of RAG. On top of these access controls, near-real-time data access logging must be present. As the RAG workloads access the data, these logs are used to inform the business if any access has changed and allows the business to easily comply with internal and external audits proving they are only using approved data sets with public LLMs and GenAI models.
Last step, keep the data secure at rest. The use of LLMs and GenAI will only accelerate the migration of sensitive data into the cloud. These data elements that were once protected on-prem will have to be protected in the cloud as well. But there is a catch. The scale requirements of this data protection will be a new challenge for businesses. You will not be able to point your existing on-prem-based encryption or tokenization solution to a cloud database like Snowflake and expect to get the full value of Snowflake.
When prospects or customers ask me, “What is ALTR’s solution for securing LLMs and GenAI” I used to joke with them and say, “Nothing!” But now I’ve learned the right response, “The same thing we’ve always done to secure your data—just with even more precision and focus for today’s challenges.” The use of LLMs and GenAI is exciting and scary at the same time. One way to reduce the anxiety is to start with a solid foundation of understanding what data you have, how that data is allowed to be used, and whether you prove that the data is safe at rest and in motion.
This does not mean you cannot use ChatGPT. It just means you must realize that you were once that careless child running with arms wide open to Mickey, but now you are the concerned parent. Your teams and company will be eager to dive headfirst into GenAI, but it’s crucial that you can articulate why this journey is complex and how you plan to guide them there safely. It begins with mastering the fundamentals and gradually tackling the tough new challenges that come with this powerful technology.

ALTR isn’t just keeping pace with the evolving data security landscape—we’re setting the speed limit. As businesses scramble to safeguard their data, ALTR is not just another player in the game; we’re the go-to solution for bulletproof data access control and security. And today, we’re doubling down on that promise with three strategic hires to turbocharge our Go-To-Market (GTM) strategy.
Christy Baldassarre joins us as our new Director of Marketing, bringing a formidable blend of strategic vision and execution prowess. With a track record of driving brand growth and market penetration, Christy excels at crafting compelling narratives that resonate with target audiences. She’s a master at turning complex concepts into clear, impactful messaging and knows how to leverage the latest digital marketing tactics to amplify ALTR’s voice.
"I am excited to be on such a great team and to be a part of taking ALTR to the next level. I chose ALTR because of its excellence in Cloud Security and Data Protection. This is a great opportunity to collaborate with such a visionary team and contribute to groundbreaking solutions that not only push boundaries but set new standards of how to keep everyone’s data safe." - Christy
Rick McBride, our new Demand Gen Manager, brings a deep expertise in go-to-market strategy. With a strong foundation in business development, Rick has honed his skills in identifying opportunities and driving pipeline growth from the ground up. He’s not just about crafting campaigns; Rick knows how to connect with decision-makers and convert interest into action.
“A successful go-to-market strategy thrives on seamless collaboration across various teams, and our GTM group is poised to be the driving force behind it. We're set to champion the Snowflake ecosystem—engaging with customers, Snowflake’s Field Sales team, and partners alike—to fuel strategic growth. By leveraging Snowflake's powerful native capabilities in Security and Governance, we aim to deliver at the speed and scale that Snowflake users expect. We're thrilled to extend this value to every organization that prioritizes and trusts Snowflake for their data management needs!” - Rick
Next, we've got George Policastro as our newest Account Executive. George is a seasoned sales professional with a proven track record of closing complex deals and delivering results. His strengths lie in his ability to deeply understand client needs, build lasting relationships, and strategically navigate the sales process to drive success.
"I’m thrilled to join ALTR and tackle one of the biggest challenges organizations face today: securing their sensitive data while unlocking its full potential to drive business growth." - George
The world of data security and governance has evolved dramatically from the days of simple perimeter defenses. Now, we’re dealing with sophisticated, multi-layered security strategies that need to keep up with cybercriminals who are more aggressive and resourceful than ever. The core principles—knowing where your data is, who can access it, and ensuring its protection—haven’t changed. However, as data moves to the cloud, the challenge is achieving these goals at an unprecedented scale and speed.
That’s where ALTR excels. We’re not just providing solutions; we’re reimagining what data access control and security can be in a cloud-first world. By cutting through the complexities and inefficiencies of traditional methods, we deliver a streamlined, scalable approach that makes data security both simple and powerful. Our intuitive automated access controls, policy automation, and real-time data observability empower organizations to protect sensitive data at rest, in transit, and in use—effortlessly and at lightning speed. With ALTR, securing your data isn’t just more accessible; it’s smarter, faster, and designed for today’s dynamic cloud environments.
With our latest GTM team expansion, we’re fortifying our foundation to evolve into a cloud data security market leader who’s not just part of the conversation but is driving it.

In a world where data breaches and privacy threats are the norm, safeguarding sensitive information is no longer optional—it's critical. As regulations tighten and privacy concerns soar, our customers are demanding cutting-edge solutions that don't just secure their data but do so with finesse. Enter Format Preserving Encryption (FPE). When paired with ALTR's capability to seamlessly share encryption keys with trusted third parties via platforms like Snowflake's data sharing, FPE becomes a game-changer.
Format Preserving Encryption (FPE) is a type of encryption that ensures the encrypted data retains the same format as the original plaintext. For example, if a credit card number is encrypted using FPE, the resulting ciphertext will still appear as a string of digits of the same length. This characteristic makes FPE particularly useful in scenarios where maintaining data format is crucial, such as legacy systems, databases, or applications requiring data in a specific format.
FPE maintains the data format, allowing easy integration into existing data pipelines without requiring significant changes. This minimizes the impact on business operations and reduces the costs associated with implementing encryption.
Many regulatory frameworks, such as the GDPR, PCI-DSS, and HIPAA, mandate the protection of sensitive data. FPE helps organizations comply with these regulations by ensuring that data is encrypted to preserve its usability and format, which can sometimes be a requirement in these standards.
Unlike traditional encryption methods, FPE allows encrypted data to be used in its existing form for specific operations, such as searches, sorting, and indexing. This ensures organizations can continue to derive value from their data without compromising security.
Snowflake is a cloud-based data warehousing platform that allows organizations to store, process, and analyze large volumes of data. One of its differentiating features is data sharing, which enables companies to share live, governed data with other Snowflake accounts in a secure and controlled manner while also shifting the cost of the computing operations of the data over to the share's consumer.
Snowflake's data sharing allows recipients to access shared data in real-time, ensuring they always have the most up-to-date information. This is particularly valuable in scenarios where timely access to data is critical, such as in financial services or healthcare.
Snowflake's platform is designed with security at its core. Data sharing is governed by robust access controls, ensuring only authorized parties can view or interact with the shared data. This is crucial for maintaining the confidentiality and integrity of sensitive information.
Snowflake's architecture allows for easy scalability, enabling organizations to share large volumes of data with multiple parties without compromising performance. Additionally, the platform supports a wide range of data formats and types, making it suitable for diverse use cases.
When FPE is combined with the ability to share encryption keys via Snowflake's data sharing, it unlocks a new level of security and flexibility for organizations. This combination addresses several critical challenges in data protection and sharing:
By leveraging FPE, organizations can encrypt sensitive data while preserving its format. However, there are scenarios where this encrypted data needs to be shared with trusted third parties, such as partners, auditors, or service providers. Through Snowflake's data sharing and ALTR's FPE Key Sharing, companies can securely share encrypted data along with the corresponding encryption keys. This allows the third party to decrypt the data within the policies that they have defined and use it as needed.
In a multi-cloud or hybrid environment, data often needs to be moved between different systems or shared with external entities. Traditional encryption methods can be cumbersome in such scenarios, as they require extensive reconfiguration or critical management efforts. However, with FPE and Snowflake's key sharing, organizations can seamlessly share encrypted data across different environments without compromising security. The encryption keys can be securely shared via Snowflake, ensuring only authorized parties can decrypt and access the data.
Many regulations require organizations to demonstrate that they have implemented appropriate security measures to protect sensitive data. By using FPE, companies can encrypt data that complies with these regulations. At the same time, the ability to share encryption keys through Snowflake ensures that data can be securely shared with auditors or regulators. Additionally, Snowflake's robust logging and auditing capabilities provide a detailed record of who accessed the data and when which is essential for compliance reporting.
In finance, healthcare, and retail industries, collaboration with external partners is often essential. However, sharing sensitive data with these partners presents significant security risks. By combining FPE with ALTR's key sharing, organizations can securely share encrypted data with partners, ensuring that sensitive information is transmitted throughout the data's lifecycle, including across shares. This enables more effective collaboration without compromising data security.
Specific data processing tasks, such as data analytics or AI model training, require access to large volumes of data. In scenarios where this data is sensitive, encryption is necessary. However, traditional encryption methods can hinder the efficiency of these tasks due to the need for decryption before processing. With FPE, the data can remain encrypted during processing, while ALTR's key sharing allows the consumer to decrypt data only when absolutely necessary. This ensures that data processing is both secure and efficient.
To better understand the value of combining FPE with ALTR's key sharing, let's explore a few use cases:
In the financial sector, organizations handle a vast amount of sensitive data, including customer information, transaction details, and credit card numbers. FPE can encrypt this data while preserving its format, ensuring it can still be used in legacy systems and applications. Through Snowflake's data sharing, financial institutions can securely share encrypted transaction data with external auditors, partners, or regulators, along with the necessary encryption keys. This ensures compliance with regulations while maintaining the security of sensitive information.
Healthcare organizations often need to share patient data with external entities, such as insurance companies or research institutions. FPE can encrypt patient records, ensuring they remain secure while preserving the format required for healthcare applications. Snowflake's data sharing allows healthcare providers to securely share this encrypted data with third parties. At the same time, ALTR enables the sharing of the corresponding encryption keys, enabling them to access and use the data while ensuring compliance with HIPAA and other regulations.
Retailers often need to share customer data with marketing partners, payment processors, or logistics providers. FPE can be used to encrypt customer information, such as names, addresses, and payment details while maintaining the format required for retail systems. Snowflake's data sharing enables retailers to securely share this encrypted data with their partners; with ALTR, the encryption keys are also shared, ensuring that customer information is always protected.
The combination of Format Preserving Encryption and ALTR's key-sharing capabilities represents a significant advancement in the field of data security. This approach addresses several critical challenges in data protection and sharing by enabling organizations to securely share encrypted data with trusted third parties.
In an increasingly interconnected world, businesses must collaborate with external partners and share data to remain competitive. However, this collaboration often comes with significant security risks. By leveraging FPE and ALTR's key sharing, organizations can strengthen trust with their partners by ensuring that sensitive data is always protected, even when shared. This leads to more effective and secure collaboration, ultimately driving business success.
Data breaches, including financial losses, reputational damage, and regulatory penalties, can devastate businesses. Organizations can significantly reduce the risk of data breaches by encrypting sensitive data with FPE and securely sharing it via Snowflake. Even if the data is intercepted, it remains protected, as only authorized parties with the corresponding encryption keys can decrypt it.
As organizations continue to innovate and leverage new technologies, such as artificial intelligence and machine learning, the need for secure data sharing will only grow. The combination of FPE and ALTR's key sharing enables businesses to securely share and process data innovatively without compromising security. This ensures that organizations can continue to innovate while protecting their most valuable asset – their data.
Integrating Format Preserving Encryption with ALTR's key sharing capabilities offers a powerful solution for organizations seeking to protect sensitive data while enabling secure collaboration and innovation. By preserving the format of encrypted data and allowing for secure key sharing, this approach addresses critical challenges in data protection, regulatory compliance, and data sharing across multiple environments. As businesses navigate the complexities of the digital age, the value of this combined solution will only become more apparent, making it a vital component of any robust data security strategy.
.png)
“Today is the day!” you exclaim to yourself as you settle into your desk on Monday morning. After months of meticulous planning, the migration from Teradata to Snowflake begins now. You have been through all the back-and-forth with leadership on why this migration is needed: Teradata is expensive, Teradata is not agile, Snowflake creates a single source of data truth, and Snowflake is instantly on and scales when you need it. It’s perfect for you and your business.
As you follow your meticulously planned checklist for the migration, you're utilizing cutting-edge tools like DBT, Okta, and Sigma. These tools are not just cool, they're the future. You're moving your database structure, loading the initial non-sensitive data, repointing your ETL pipelines, and witnessing the power of modern technology in action. Everything is working like a charm.
A few weeks or months of testing go by, your downstream consumers of data are still using Teradata but are starting to give thumbs up on the Snowflake workloads that you have already migrated. Things are going well. You have not thought about CPU or disk space for the Teradata box in a while, which was the point of the migration. You finally get word from all stakeholders that this trial migration was a success! You call your Snowflake team, and tell them to back up the truck, you are clear to move the remaining workloads. Life is good. But then, comes a knock at the door.
It’s Pat from Security & Risk. You know Pat well and enjoy Pat’s company, but you also do as much as possible to avoid Pat because you are in data and, well, we all know the feeling. Pat tells you, “Heard we are finally getting off Teradata; that’s awesome! Do you have a plan for the PII and SSNs that are kept in that one Teradata database that we require using Protegrity for audit and compliance reasons?” You nod, “I do, but I couldn't do it without your expertise. I’ve been reading the Snowflake documentation, and I'm in the process of writing a few small AWS Lambdas to interface with Protegrity. Your input is crucial to this process.” Pat smiles, gives a non-assuring hand on your back and walks out. Phew, no more Pat.
Four weeks later, you're utterly exhausted. You've logged over 50 hours in Snowflake with fellow data engineers, and tapped into the expertise of one of the cloud ops team members who knows Lambda inside out. You have escalated to Snowflake support, but your external function calls from Snowflake to AWS keep timing out. AWS support is unable to help. Now, you have memory limits being hit with AWS Lambda. Suddenly, the internal network team does not want to keep the ports open to hit Protegrity from AWS, and you need to use a Private Link connection with additional security controls. You are behind on the Teradata migrations. There is no end in sight of the scale problems. Shoot, this is not working.
Don’t worry, you are not alone. This is the same experience felt by hundreds of Snowflake customers, and it stems from the same problem: everything about your Snowflake migration was planned for the new architecture of Snowflake except for one thing: data protection. You followed all the blogs and user guides, and your stateless data pipeline feeding Snowflake with a Kafka bus is perfect. Sigma is running without limits. The team is happy, but they want that customer data now. Except, you can’t use it until you solve this security problem.
Snowflake and OLAP workloads, generally, turned data protection on its head. OLTP workloads are easy to secure. You know the access points and the typical pattern of user behavior, so you can easily plan for scale and up-time. OLAP is widely unpredictable. Large queries, small queries, ten rows, 10M rows, it’s a nightmare for security. There is only one path forward: you must get purpose-built data protection for Snowflake.
You need a data protection solution that matches Snowflake’s architecture, just like when you matched Protegrity to Teradata. If Snowflake is going to be elastic, your data protection needs to be elastic. If Snowflake is going to be accessed by many downstream consumers, you need to be able to integrate data protection into the access policies in Snowflake. Who is going to do that work? Who will maintain this code? How can you control costs? The answer to all those questions is ALTR.
ALTR’s purpose-built native app for data protection is an easy solution for Snowflake. You can install it on your own. You can use your Snowflake committed dollars to pay for the service. ALTR’s data protection scale is controlled by Snowflake and nothing else. It’s the easiest way to get back on track. Call your Snowflake team, ask them about ALTR. It will feel good walking back into Pat’s office with your head held high and your data migration back on track.
Whether your team currently has Protegrity or Voltage, you will face the same problems. Do not waste your time trying to get these solutions to scale, just call ATLR.
Don’t just take my word for it…

In a world where data is the lifeblood of organizations, managing and securing that data is no longer just an IT task—it's a business imperative. Yet, despite the critical nature of data governance, many solutions out there are still bogged down by complexity, time-consuming processes, and significant risks. Enter ALTR, the cutting-edge solution that’s not just simplifying data governance but revolutionizing it. Here’s why ALTR is the game-changer your organization needs, and why it’s quickly becoming the go-to for companies leveraging Snowflake.
Data governance has long been a domain reserved for the technically savvy, with traditional methods requiring extensive SQL coding and intricate configurations. This not only made the process time-consuming but also left it vulnerable to human error. ALTR redefines this narrative with a user-centric approach. Seamlessly integrated into Snowflake and instantly accessible through Snowflake Partner Connect, ALTR is designed to be up and running in mere minutes. The intuitive interface, built on ALTR’s robust Management API, empowers even non-technical users to accomplish tasks that once required days of coding—now achievable with just a few clicks. ALTR democratizes data governance, making it fast, simple, and accessible to all, ensuring that security is no longer a complex or exclusive domain, but one that everyone can master.
In the high-speed world of data, there's simply no room for delay. ALTR recognizes this need for urgency, delivering Proof of Value and Time to Value in a matter of hours and days—rather than the months or quarters typical of traditional solutions. With ALTR’s SaaS model, you can unlock its features in your Snowflake sandbox environment at no cost, letting you experience its power before making any commitments.
But ALTR doesn’t just stop at providing tools; we empower you with expertise. Our team of Field Engineers is ready to assist in crafting tailored solutions, automating processes, and ensuring seamless interoperability with your data catalogs, ETL/ELT tools, and SIEMs. Customers often leverage ALTR’s Rapid POC Framework, which accelerates the definition of use case requirements and success criteria. Over just two or three focused one-hour screenshare sessions with an ALTR Field Engineer, you’ll produce the artifacts, evidence, and performance metrics needed to confidently move toward full-scale implementation.
It’s not merely about demonstrating ALTR’s value—it’s about ensuring you realize that value at lightning speed, setting your team up for swift, scalable success.
In the realm of data governance and security, complexity is the silent killer. The more convoluted your protocols, the more they drain your resources—whether that’s time, money, or manpower. ALTR was engineered to dismantle this complexity from the ground up. Managing access policies across multiple access points like SNOW SQL, BI Tools, applications, and data shares is an overwhelming task on its own. When you add the intricacies of data security within Snowflake’s ecosystem, the challenge becomes even more daunting. ALTR alleviates these burdens by enabling automation at scale and empowering users to handle these tasks with ease. By simplifying these traditionally complex processes, ALTR doesn't just reduce friction; it eliminates the barriers that have historically plagued data governance. With ALTR, complexity is no longer an obstacle—it's a thing of the past.
Human error is the Achilles’ heel of data security. From misconfigurations to overlooked details, the potential for mistakes is vast. Recent Snowflake Security incidents serve as stark reminders of these risks. ALTR addresses this vulnerability head-on. By eliminating the need for manual SQL scripting and enabling point-and-click automation, ALTR significantly reduces the risk of human error. But it doesn’t stop there. ALTR’s advanced Data Protection features—such as Format-Preserving Encryption and Tokenization—ensure that your data is protected at rest, in transit, and even in use. Coupling this with access policy automation means your data is safe from external threats, internal misuse, and even potential risks from privileged users.
In today’s data-driven world, interoperability isn’t just a nice-to-have; it’s essential. ALTR’s SaaS architecture is designed to work seamlessly within your existing data ecosystem and InfoSec stack, making it an ideal partner for your CISO’s peace of mind. Whether it’s leveraging Snowflake Object Tags or integrating with your SIEM, SOAR, or workflow resolution software, ALTR ensures everything works together flawlessly. By making real-time Data Activity Monitoring logs, policy alerts, and notifications available within your existing systems, ALTR takes interoperability to the next level, ensuring that your data governance is as efficient as it is secure.
ALTR is not just another data governance tool—it’s a revolution in how data is managed and secured. By focusing on ease of use, rapid proof of value, reduced complexity, minimized risk, and seamless interoperability, ALTR is setting a new standard in the industry. For companies leveraging Snowflake, ALTR is the key to unlocking the full potential of their data while safeguarding it from the ever-present threats of today’s digital landscape. In a world where data is king, ALTR is the crown. Don’t just manage your data security—master it with ALTR.

Keeping a tight grip on data access control is crucial for protecting sensitive information. However, when these systems get too complicated, they can bring about a whole host of challenges and additional risks. If you're finding that your data access control is more headache than help, it might be time to take a closer look. Let's explore ten signs that your data access control might be overly complex and explore some practical solutions to help streamline and strengthen your data security approach.
Are you experiencing persistent configuration errors? This may indicate an overly complex data access control system. These errors often arise from the intricate setup and continuous and manual adjustments needed to manage permissions. When systems require detailed and specific configurations, even minor mistakes can lead to significant vulnerabilities. Frequent misconfigurations are a security risk and a drain on resources, necessitating constant oversight and corrections.
Is your team struggling to respond to access requests or security incidents promptly? This suggests your system is too convoluted. The more complex the system, the harder it is for security teams to act swiftly and efficiently. Complex workflows and multiple layers of approval can slow down response times, increasing the risk of security breaches going undetected or unaddressed for extended periods.
Excessive resources spent on maintaining and updating access controls indicate unnecessary complexity. High maintenance costs often stem from the need for specialized training and continuous updates to keep the system running smoothly. These costs add up quickly, diverting funds and constrained resources from other critical areas, making the system financially unsustainable over the long term.
Are you using multiple tools to manage access control? This can create redundancies, integration issues and make the system harder to manage and more expensive to maintain. Each tool requires its own configuration, management, and monitoring, adding layers of complexity that can overwhelm security teams.
Is your security team struggling to monitor access in real-time? This could be a sign of system complexity and can lead to undetected breaches and delayed responses. Complex systems generate vast amounts of data, making it challenging to filter out critical security alerts from the noise. Ineffective real-time monitoring can result in slow threat detection and response times, increasing the risk of significant security incidents.
Wide variations in access control policies across different parts of the organization can lead to security gaps and enforcement inconsistencies. Ensuring a unified security approach becomes challenging when other departments or teams use different policies. Attackers who look for weak spots in the security fabric can exploit this inconsistency.
Are you struggling to conduct regular audits and ensure compliance with industry regulations? This could indicate that your access control processes are too complex. The intricate nature of these systems often requires specialized knowledge to navigate and assess, making compliance audits time-consuming and costly. Non-compliance can expose the organization to legal and financial risks, including fines and reputational damage.
Complex access controls can make monitoring and restricting insider access difficult, leading to a higher incidence of insider threats. Insiders who already have a level of trusted access can exploit overly complex systems to bypass security measures or access unauthorized data. The difficulty in tracking and managing insider activities in such environments exacerbates this risk.
Are users struggling to get the access they need to data? This indicates overly complex access controls, which can decrease productivity and lead to frustration. This can also lead to users seeking workarounds, such as using unauthorized methods to access data, which further compromises security.
Selecting the right Data Security Platform (DSP) is crucial for effectively managing data access control and safeguarding sensitive information. Here are the key attributes to consider when choosing a DSP:
A robust DSP should offer automated tools for quickly identifying and classifying sensitive data. This capability ensures that high-risk data is discovered and protected promptly, meeting compliance requirements. Automated classification tools help streamline the identification process, reducing the manual effort involved and ensuring that all sensitive data is accounted for and adequately secured.
Look for a DSP that allows you to set up automated access controls with dynamic data masking capabilities. These controls ensure that only credentialed users can access sensitive information, minimizing the risk of unauthorized access. They also help maintain security policies consistently across the organization, reducing the potential for human error and enhancing overall data protection.
Effective DSPs provide real-time observability over how sensitive data is consumed in the cloud. This includes active alerts for unauthorized requests, allowing immediate response to potential security breaches. Real-time data activity monitoring is essential for maintaining an up-to-date security posture and ensuring that any suspicious activity is detected and addressed promptly.
Choose a DSP that offers integrated data security from source to cloud. Automated data access governance ensures that sensitive data is never at risk, providing comprehensive protection throughout its lifecycle. Integrated security measures help unify the approach to data protection, ensuring that all aspects of data security are covered and reducing the complexity involved in managing multiple security tools.
A good DSP should allow non-technical users to implement policies and simplify data ownership. This ensures that data security processes can remain streamlined and automated without requiring extensive technical knowledge. User-friendly interfaces and straightforward policy implementation tools enable broader participation in data governance, helping to maintain consistent security practices across the organization.
Managing data access control is vital for protecting sensitive information, but complexity can create numerous risks and challenges. By recognizing the signs and choosing the right Data Security Platform (DSP), you can create more robust and manageable data security environment.

In a previous post, Jonathan Sander details the primary differences between a Data Security Posture Management (DSPM) solution and a Data Security Platform (DSP). He highlights that the most notable difference between a DSPM and a DSP is in the “policy definition and policy enforcement” aspects of a DSP. He explains that while some applications allow for simple API calls to manage access or security policies, such as removing a user’s group membership in Active Directory, implementing policy definition and enforcement at a deeper level for platforms like Snowflake becomes exceedingly challenging, if not impossible, for a DSPM.
Recent events have reignited my interest in understanding how ALTR distinguishes itself from a DSPM. The first event was the potential acquisition of Wiz by Google. Wiz, a cloud security posture management (CSPM) tool, is often confused with a DSPM. This has led customers to inquire about the differences between CSPM and DSPM and, subsequently, the distinctions between DSPM and DSP. Although the Wiz/Google deal fell through, it sparked an insightful discussion on Linkedin initiated by Pramod Gosavi from JupiterOne. I participated in this discussion, which delved into why Google should reconsider buying a tool like Wiz.
The other recent event that brings DSPM v DSP back into spotlight is the word ‘remediation’, which has been used by some DSPM providers lately. The word remediation in this context indicates a DSPMs ability to react to one of their findings. For example, a remediation might be removing a user’s access from a system or making a public-facing internet resource private. These types of remediations are simple and straightforward and should easily be achievable by a DSPM. But lately, some of the DSPM players have been making mention of remediations for platforms like Snowflake stating their platforms can do complex operations such as RBAC, data masking, and data security such as encryption or tokenization. This is where the analogy "All squares are rectangles, but not all rectangles are squares" comes in handy. In this scenario, the DSPM is the square, and the DSP is the rectangle. A DSP can perform all the functions of a DSPM, but a DSPM cannot perform all the functions of a DSP. Let me explain.
The largest difference between a DSPM and a DSP is not the type or number of data stores supported, or the workflows within the platforms, but rather the biggest difference is the integration methods with the data stores. DSP’s live in the line of fire. We sit in the hardest place a vendor can sit, in the critical path of data. It’s the only way a DSP can provide capabilities like real-time database activity monitoring (DAM), data encryption or tokenization, data loss prevention, and others. Without this position in the stack, our ability to stop, or remediate, an out of policy data access request is minimized.
DSPM’s on the other hand do not live in the critical path of data access. They often exist outside the normal access patterns connecting to systems such as databases or file shares without fear of latency or uptime. A DSP has the unfortunate burden of having to essentially match the uptimes and availability of the platforms they control, often requiring significant investments in engineering and operations that DSPM do not have. It's these requirements of uptime, throughput, and strict performance metrics that make it nearly impossible for a DSPM to offer value over a DSP when it comes to complex operations in a platform like Snowflake. Since a DSP is already in line with the systems they are controlling and protecting, it is conceivable that a DSP could offer a wide overlap of the features of a DSPM, if it wanted to.
For customers, this means taking the time to understand the specific challenges you need to address for platforms like Snowflake, particularly regarding access controls and security. The multiple layers of roles and attributes assigned to users, the vast amount of data that moves and transforms inside the Snowflake platform daily, and the performance requirements of encryption on your downstream application is complex. These are hard problems for any business. And solving these challenge is what is going to fully unlock the value of your Snowflake instance.
Be cautious of any DSPM that claims to solve the complex governance and security challenges of Snowflake effortlessly. Always request detailed case studies to validate their claims. While it's not necessarily impossible, these claims often resemble a square trying to fit into a rectangle.

Data is the fuel propelling modern business. From customer information to financial records, proprietary data forms the foundation upon which businesses operate and innovate. However, as companies grow and data volumes explode, securing this data becomes exponentially more complex. This is where the importance of scalability in data security comes into sharp focus.
Scalability in data security is not a luxury; it is a necessity. As organizations expand, they generate and collect vast amounts of data. This growth demands a data security solution that can scale seamlessly with the volume, velocity, and variety of data. Organizations expose themselves to heightened risks, increased vulnerabilities, and potential catastrophic breaches without scalable security measures.
To understand the nuances of scalable security, we must delve into its core pillars: flexibility, performance, automation, and comprehensive coverage.
Flexibility is the cornerstone of scalable security. A rigid security solution that cannot adapt to changing needs and expanding data environments is destined to fail. Scalable security solutions must be flexible enough to integrate with a wide array of data sources, applications, and infrastructures, whether on-premises, in the cloud, or hybrid environments.
Flexibility also means accommodating varying security policies and compliance requirements. As regulations evolve and new threats emerge, a scalable security platform must allow for rapid adjustments to policies and controls without disrupting operations.
As data volumes grow, maintaining performance is crucial. Security measures that introduce latency or degrade performance are counterproductive and can hinder business operations and user experience. Scalable data security solutions must be designed to handle high throughput and large-scale environments without compromising o speed or efficiency.
Performance in scalable security also involves optimizing resource utilization. Efficient use of computational resources ensures that security operations, such as encryption, decryption, and monitoring, do not become bottlenecks as data scales.
Automation is a critical component of scalability in data security. Manual processes are time-consuming, error-prone, and incapable of keeping up with the dynamic nature of modern data environments. For instance, manually writing and maintaining SQL queries for data access control can be labour-intensive and prone to mistakes. Scalable security platforms leverage automation to ensure continuous protection without requiring constant human intervention.
Automated access policies, tokenization, and policy enforcement allow organizations to scale their security operations in line with their data growth. This automation enhances security posture and frees up valuable human resources to focus on strategic initiatives.
Scalable security requires comprehensive coverage across all data assets and environments. It is insufficient to secure only certain parts of the data ecosystem while leaving others vulnerable. A genuinely scalable security solution provides end-to-end protection, encompassing data at rest, in transit, and use.
Comprehensive coverage also means detecting and mitigating threats across the entire attack surface. This includes monitoring for insider threats, external attacks, and vulnerabilities within the data infrastructure. Scalable security platforms employ advanced analytics and machine learning to provide real-time insights and proactive threat management.
The complexity of scalable security lies in its ability to balance the varying demands of growth, performance, and protection. Here are some critical nuances to consider:
Scalable security solutions must be designed with future growth in mind. This involves anticipating the increase in data volume and users, the evolution of threat landscapes, and regulatory requirements. Future-proofing ensures that security investments remain practical and relevant as the organization evolves.
Interoperability is critical in a diverse data ecosystem. Scalable security platforms must seamlessly integrate with existing tools, applications, and processes. This integration capability ensures that security measures do not operate in silos but rather enhance the overall security posture through cohesive and collaborative defenses.
As data scales, so do the costs associated with securing it. Scalable security solutions must provide a cost-effective approach to protection, balancing the need for robust security with budget constraints. One approach is to leverage native architectures to manage costs effectively.
The consequences of failing to implement scalable security measures are dire. As data grows unchecked by scalable security, organizations face an increased risk of data breaches, regulatory fines, and reputational damage. Here are some potential pitfalls:
Without scalable security, the likelihood of data breaches increases significantly. Cybercriminals exploit vulnerabilities in outdated or inadequate security measures, leading to unauthorized access, data theft, and financial losses.
Data protection regulations are becoming increasingly stringent. Organizations that fail to scale their security measures in accordance with these requirements risk non-compliance, which can result in hefty fines and legal repercussions.
Inadequate security stability can lead to operational disruptions. Performance bottlenecks, system downtime, and compromised data integrity can impede business operations, leading to loss of productivity and revenue. Additionally, when security measures fail to scale, legitimate users may be unable to access critical data, causing further delays and hindering decision-making processes. This not only frustrates employees but also hampers overall business efficiency and agility.
In a world where data is both a valuable asset and a potential liability, the importance of scalable security cannot be overstated. As businesses continue to expand and generate more data, the need for robust, scalable security measures will only become more critical. Embracing scalable security is about protecting data today and preparing for tomorrow's challenges. The time to act is now.